Engage takes away the hard process of securing your business
Penetration testing is the practice of testing a computer system, network or web application to find security vulnerabilities that an attacker could exploit.
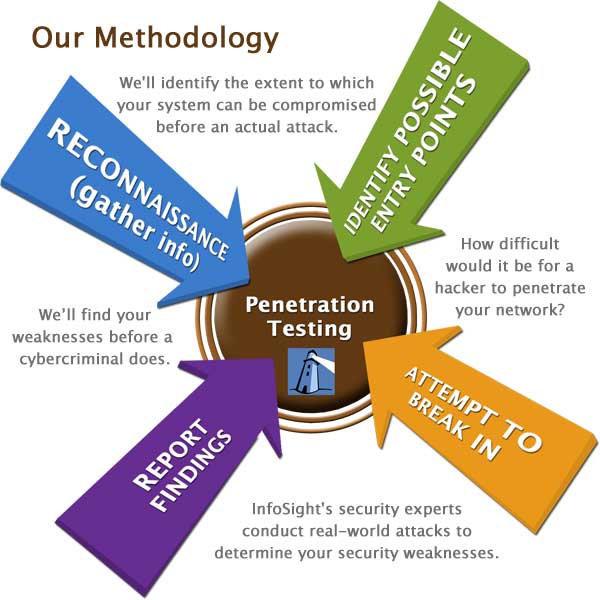
Penetration testing involves gathering information about the target before the test, identifying possible entry points, attempting to break in -- either virtually or for real -- and reporting back the findings.
Penetration testing is a detailed, and comprehensive form of testing that is often broken down into several part's and is performed over a certain allowed period of time.
The reports generated by a penetration test provide the feedback needed for an organization to prioritize the investment it plans to make in its security.
Share risk and control data across your organization. Link strategic risk to today’s operations and save weeks of report preparation.
Comparison of Vulnerability Assesment and Penetration Testing
| Vulnerability Assessment | Penetration Testing | |
|---|---|---|
| Working | Discover Vulnerabilities | Identify and Exploit Vulnerabilities |
| Mechanism | Discovery & Scanning | Simulation |
| Focus | Breadth over Depth | Depth over Breadth |
| Coverage of Completeness | High | Low |
| Cost | Low-Moderate | High |
| Performed By | In-house Staff | An Attacker or Pen Tester |
| Tester Knowledge | High | Low |
| How often to Run | Quarterly | Once per year |
| Result | Provide Partial Details about Vulnerabilities | Provide Complete Detailsof Vulnerabilities |